Intro
For years, DevOps has been the crucial link between development and operations — powering automation, continuous delivery, and secure, fast‑moving engineering. But as organizations push developers to become full‑stack and embrace shift‑left practices, the traditional DevOps role is becoming diluted. Developers are now expected to build features, deploy them, and manage pipelines, often without deep operational or security experience.
This shift brings speed and autonomy, but also risk. Inexperienced engineers can unintentionally create security back doors in CI/CD workflows — a concern Microsoft highlights, warning that Azure DevOps pipelines can become unintentional security vulnerabilities if not properly governed (Source: Microsoft Learn – End-to-End Governance in Azure CI/CD)
The Quiet Casualties of Shift‑Left: The Things That Get Forgotten
When inexperienced developers are thrust into DevOps territory certain practices are often omitted – not out of negligence, but inexperience.
Some of the first casualties include:
SAST (Static Application Security Testing)
Its important to build this into automated pipelines to scan code vulnerabilities – analyzing structure, logic and data flow of code to find insecure patterns such as SQL, XML injection, XSS, authentication and authorization flaws e.g. hardcoded credentials, weak authentication logic, insecure API’s, poor error handling.
SCA (Software Composition Analysis)
Again built into pipelines to scans for third party and open source dependencies e.g. libraries, packages that may have vulnerabilities, be outdated or unpatched, have published CVE’s (Common Vulnerabilities and Exposures) or may potentially result in licensing conflicts
DAST (Dynamic Application Security Testing)
Testing your application the same way an attacker would—from the outside, interacting with the UI, APIs, authentication flows, and runtime behavior. Built directly into your pipeline.
Secret Scanning
Without governance, secrets slip into repos — especially among inexperienced pipeline creators.
Branch Policies
Prevent reviewer requirements being skipped, build validation, and status checks if they aren’t enforced
Pre-deployment approvals
Developers unfamiliar with release management often bypass environment approvals, inadvertently granting wide deployment privileges.
Why Governance Becomes Critical in This New Landscape
Governance doesn’t exist to slow teams down — it exists because modern distributed teams need consistent guardrails, especially when experience levels vary.
Modern DevSecOps guidance stresses that security must be continuous, automated, and embedded early — not an afterthought. This includes integrating static analysis, continuous scanning, and policy enforcement directly into the DevOps pipeline.
Shift‑left security also requires tooling that enforces scanning, policy controls, and compliance checks throughout the SDLC
Governance frameworks ensure that no matter who builds a pipeline, it meets the organization’s standards for security, compliance, and reliability.
Quick Wins You Can Implement Tomorrow
Not all governance improvements require major organizational changes. Some wins are immediate and high‑impact.
I’ve adopted several of these approaches myself to mitigate for some of the less DevOps minded engineers in Azure DevOps – and they’ve proven valuable in real‑world delivery.
However, it’s important to acknowledge that there is no one‑size‑fits‑all model. These tactics should be shaped around your team’s workflows, culture, and delivery practices so they enhance — rather than obstruct — how your organization operates.
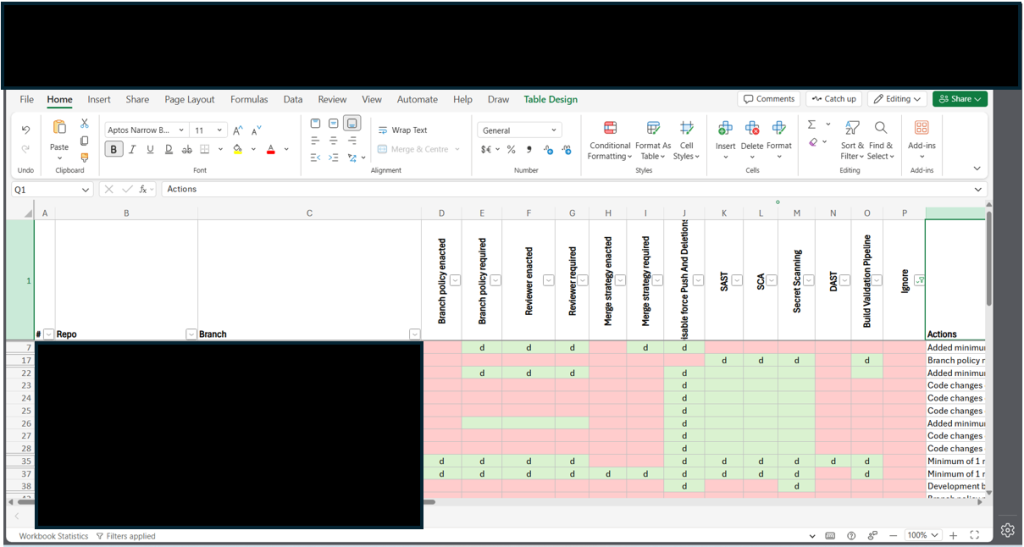
✔ Governance Gap Analysis
First things first – get organised. Map out the topology of the repos and branches, identify where the remediations should be targeted and focus your efforts whilst updating your status as you go. A simple spreadsheet similar to the below can help especially when sharing information
✔ Add SAST and SCA scanning as mandatory pipeline steps
Shift‑left security starts here. Where you possible – create centralized templates with built in SAST and SCA tasks and indirectly enforce that they are used/extended by all developers with branch policies. Pretty straight forward with Github Advanced Security, a few check boxes to enable the service and then update any pipelines with a couple of build tasks where you want the build to break if there are any violations.
✔ Add required PR reviewers on all protected branches
This instantly prevents dangerous merges by inexperienced devs. Enforce that all comments should be resolved and link and commits to tasks to give the reviewer context.
✔ Add build validation as a required check
A broken or insecure pipeline can’t merge without passing CI. You can implement a build pipeline with SAST and SCA scans here and if its not a shared validation pipeline you can also run any automated tests.
✔ Enable secret scanning in all repos
Catch exposed credentials before they reach production. Enable at repository level. GitHub Advanced Security has push protection to prevent secrets even being committed.
✔ Use environment approvals for Production
Prevent accidental (or unauthorized) deployments. Use pre-deployment approvals.
✔ Convert all pipelines to YAML templates
Within weeks, you can standardize everything from builds to releases.
✔ Apply RBAC properly
One of the highest risk areas in Azure DevOps.
These are low effort, extremely high value steps that close common back doors quickly.
Microsoft suggests adopting RBAC style principles such as applied with Azure Resource Manager
- Limit developers to deploy to dev/test environments
- Only admins can approve production deployments
- Control Service Connection configuration
An Implementation Story
To support the above theory I have followed up with a 3 part series demonstrating some of the above practices in action.
- Part 1: Tooling, Secret Scanning, and Branch Protection Strategies
- Part 2: Static Analysis Software Testing (SAST), Software Composition Analysis (SCA) and Build Pipelines
- Part 3: Implementing Dynamic Application Security Testing (DAST) in Build Pipelines
Summary
As developers take on more DevOps responsibilities, the risk of misconfiguration and security vulnerabilities increases dramatically — but only if organizations fail to establish proper governance.
Shift‑left is about moving responsibility earlier — with guardrails.
By centralizing templates, enforcing branch protections, integrating automated security scanning, aligning RBAC style principles, and restricting production access, organizations can empower developers without sacrificing security.
Leave a Reply